We are using intune to deploy the Sophos Connect Client for VPN-Connections to our users. We built a msi package, uploaded it to intune (App install context: device) and deploy it to a group of devices. I really liked Sophos MDM for basic app control and device inventory for iOS and Android devices. We also use Jamf for Mac OS deployment (thru their Device Enrolment Program) and device inventory and don’t plan on getting rid of it just because we’ll be using another inventory system. Note: The content of this article has been moved to Sophos Central Windows Endpoint: Deploying using Microsoft Intune Sign up to the Sophos Support Notification Service to get the latest product release information and critical issues. Microsoft Intune is ranked 1st in Enterprise Mobility Management (EMM) with 18 reviews while Sophos Mobile is ranked 11th in Enterprise Mobility Management (EMM) with 2 reviews. Microsoft Intune is rated 7.6, while Sophos Mobile is rated 7.0. Sophos Intercept X for Mobile can be centrally configured from Sophos Central, which hosts our Unified Endpoint Management (UEM) platform. Deployment can occur via existing app stores with user enrolment, or the app can be pushed using existing UEM’s such as Sophos Mobile or third-party Enterprise Mobility Management (EMM) tools.
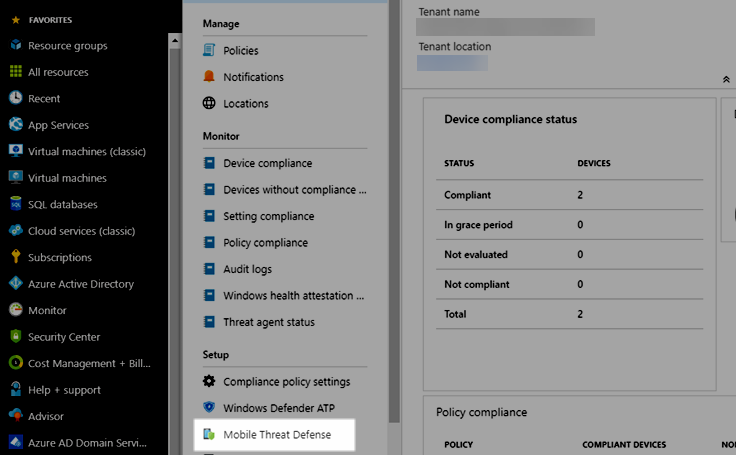
-->You can control mobile device access to corporate resources using Conditional Access based on risk assessment conducted by Sophos Mobile, a Mobile Threat Defense (MTD) solution that integrates with Microsoft Intune. Risk is assessed based on telemetry collected from devices running the Sophos Mobile app.You can configure Conditional Access policies based on Sophos Mobile risk assessment enabled through Intune device compliance policies, which you can use to allow or block noncompliant devices to access corporate resources based on detected threats.
Note
This Mobile Threat Defense vendor is not supported for unenrolled devices.

Supported platforms
- Android 6.0 and later
- iOS 11.0 and later
Prerequisites
- Azure Active Directory Premium
- Microsoft Intune subscription
- Sophos Mobile Threat Defense subscription
For more information, see the Sophos website.
How do Intune and Sophos Mobile help protect your company resources?
Sophos Mobile app for Android and iOS/iPadOS captures file system, network stack, device, and application telemetry where available, and then sends the telemetry data to the Sophos Mobile cloud service to assess the device's risk for mobile threats.
The Intune device compliance policy includes a rule for Sophos Mobile Threat Defense, which is based on the Sophos Mobile risk assessment. When this rule is enabled, Intune evaluates device compliance with the policy that you enabled. If the device is found noncompliant, users are blocked access to corporate resources like Exchange Online and SharePoint Online. Users also receive guidance from the Sophos Mobile app installed in their devices to resolve the issue and regain access to corporate resources.
Sample scenarios
Here are some common scenarios.
Control access based on threats from malicious apps
When malicious apps such as malware are detected on devices, you can block devices from the following actions until the threat is resolved:
- Connecting to corporate e-mail
- Syncing corporate files with the OneDrive for Work app
- Accessing company apps
Block when malicious apps are detected:
Access granted on remediation:
Control access based on threat to network
Detect threats to your network like Man-in-the-middle attacks, and protect access to Wi-Fi networks based on the device risk.
Block network access through Wi-Fi:


Access granted on remediation:
Control access to SharePoint Online based on threat to network
Sophos Intune Antivirus
Detect threats to your network like Man-in-the-middle attacks, and prevent synchronization of corporate files based on the device risk.
Block SharePoint Online when network threats are detected:
Access granted on remediation:
Next steps
-->When using Intune to provision devices with certificates to access your corporate resources and network, use a trusted certificate profile to deploy the trusted root certificate to those devices. Trusted root certificates establish a trust from the device to your root or intermediate (issuing) CA from which the other certificates are issued.
You deploy the trusted certificate profile to the same devices and users that receive the certificate profiles for Simple Certificate Enrollment Protocol (SCEP), Public Key Cryptography Standards (PKCS), and imported PKCS.
Export the trusted root CA certificate
To use PKCS, SCEP, and PKCS imported certificates, devices must trust your root Certification Authority. To establish trust, export the Trusted Root CA certificate, and any intermediate or issuing Certification Authority certificates, as a public certificate (.cer). You can get these certificates from the issuing CA, or from any device that trusts your issuing CA.
To export the certificate, refer to the documentation for your Certification Authority. You'll need to export the public certificate as a .cer file. Don't export the private key, a .pfx file.
You'll use this .cer file when you create trusted certificate profiles to deploy that certificate to your devices.
Sophos Microsoft
Create trusted certificate profiles
Create and deploy a trusted certificate profile before you create a SCEP, PKCS, or PKCS imported certificate profile. Deploying a trusted certificate profile to the same groups that receive the other certificate profile types ensures that each device can recognize the legitimacy of your CA. This includes profiles like those for VPN, Wi-Fi, and email.
SCEP certificate profiles directly reference a trusted certificate profile. PKCS certificate profiles don't directly reference the trusted certificate profile but do directly reference the server that hosts your CA. PKCS imported certificate profiles don't directly reference the trusted certificate profile but can use it on the device. Deploying a trusted certificate profile to devices ensures this trust is established. When a device doesn't trust the root CA, the SCEP or PKCS certificate profile policy will fail.
Create a separate trusted certificate profile for each device platform you want to support, just as you'll do for SCEP, PKCS, and PKCS imported certificate profiles.
Important
Trusted root profiles that you create for the platform Windows 10 and later, display in the Microsoft Endpoint Manager admin center as profiles for the platform Windows 8.1 and later.
This is a known issue with the presentation of the platform for Trusted certificate profiles. While the profile displays a platform of Windows 8.1 and later, it is functional for Windows 10 and later.
Note Discourse disable markdown.
The Trusted Certificate profile in Intune can only be used to deliver either root or intermediate certificates. The purpose of deploying such certificates is to establish a chain of trust. Using the trusted certificate profile to deliver certificates other than root or intermediate certificates is not supported by Microsoft. You might be blocked from importing certificates which are not deemed to be root or intermediate certificates when selecting the trusted certificate profile in the Microsoft Endpoint Manager admin center. Even if you are able to import and deploy a certificate which is neither a root or intermediate certificate using this profile type, you will likely encounter unexpected results between different platforms such as iOS and Android.
Trusted certificate profiles for Android device administrator
Beginning with Android 11, you can no longer use a trusted certificate profile to deploy a trusted root certificate to devices that are enrolled as Android device administrator. This limitation doesn't apply to Samsung Knox.
Because SCEP certificate profiles require both the trusted root certificate be installed on a device, and must reference a trusted certificate profile that in turn references that certificate, use the following steps to work around this limitation:
Manually provision the device with the trusted root certificate. For sample guidance, see the following section.
Deploy to the device, a trusted root certificate profile that references the trusted root certificate that you’ve installed on the device.
Deploy a SCEP certificate profile to the device that references the trusted root certificate profile. Screenfocus.
This issue isn’t limited to SCEP certificate profiles. Therefore, plan to manually install the trusted root certificate on applicable devices should your use of PKCS certificate profiles, or PKCS Imported certificate profiles require it.
Learn more about changes in support for Android device administrator from techcommunity.microsoft.com.
Manually provision a device with the trusted root certificate
The following guidance can help you manually provision devices with a trusted root certificate.
Download or transfer the trusted root certificate to the Android device. For example, you might use email to distribute the certificate to device users, or have users download it from a secure location. After the certificate is on the device, it must be opened, named, and saved. Saving the certificate adds it to the User certificate store on the device.
- To open the certificate on the device, a user must locate and tap (open) the certificate. For example, after sending the certificate by email, a device user can tap on or open the certificate attachment.
- When the certificate opens, the user must provide their PIN or otherwise authenticate to the device before they can manage the certificate.
After authentication, the certificate opens and must be named before it can be saved to the Users certificate store. The certificate name must match the certificate name that’s specified in the Trusted Root Certificate profile that will be sent to the device.After naming the certificate, it can be saved.
After being saved the certificate is ready for use. A user can confirm the certificate is in the correct location on the device:
- Open Settings > Security > Trusted credentials. The actual path to Trusted credentials can vary by device.
- Open the User tab and locate the certificate.
- If present in the list of User certificates, the certificate is installed correctly.
With a root certificate installed on a device, you must still deploy the following to provision the SCEP or PKCS certificates:
- A Trusted Certificate profile that references that certificate
- The SCEP or PKCS profile that references the certificate profile to provision the SCEP or PKCS certificates.
To create a trusted certificate profile
Sign in to the Microsoft Endpoint Manager admin center.
Select and go to Devices > Configuration profiles > Create profile.
Enter the following properties:
- Platform: Choose the platform of the devices that will receive this profile.
- Profile: Select Trusted certificate. Or, select Templates > Trusted certificate.
Select Create.
In Basics, enter the following properties:
- Name: Enter a descriptive name for the profile. Name your profiles so you can easily identify them later. For example, a good profile name is Trusted certificate profile for entire company.
- Description: Enter a description for the profile. This setting is optional, but recommended.
Select Next.
In Configuration settings, specify the .cer file for the trusted Root CA Certificate you previously exported.
For Windows 8.1 and Windows 10 devices only, select the Destination Store for the trusted certificate from:
- Computer certificate store - Root
- Computer certificate store - Intermediate
- User certificate store - Intermediate
Select Next.
In Assignments, select the user or groups that will receive your profile. For more information on assigning profiles, see Assign user and device profiles.
Select Next.
(Applies to Windows 10 only) In Applicability Rules, specify applicability rules to refine the assignment of this profile. You can choose to assign or not assign the profile based on the OS edition or version of a device.
For more information, see Applicability rules in Create a device profile in Microsoft Intune.
In Review + create, review your settings. When you select Create, your changes are saved, and the profile is assigned. The policy is also shown in the profiles list.
Next steps
Create certificate profiles:

Learn about Certificate connectors
